insights & resources
Our 2024 UK Salary Guide is Here!
In the ever-advancing world of technology, staying ahead of the latest trends and insights is key for both job seekers and employers. As we step into 2024, the state of the UK tech job market continues to change. Recovering from the post-COVID hiring boom, the market continues to adjust and stabilise. Navigating this landscape can be difficult. To guide you, we are excited to launch our much-anticipated 2024 UK Salary Guide. Encompassing the data taken from roughly 3600 hires across 25 industries in 2023, we have created this comprehensive guide filled with market insights and our experts’ predictions across our specialisms of Data, AI & Machine Learning, Product, Software, Cloud, and Cyber. As well as a spotlight on the C-Suite level.
Analysing Salary Benchmarks:
Our 2024 Salary Guide provides the average salaries for different roles at all levels across our key specialisms. From Data Engineering to Golang Developers, End-User Computing to IAM Architects, and everything in between, we dive into all the compensation trends. Whether you're a newcomer to the UK tech scene or a seasoned professional eyeing executive positions, our guide offers an overview of salary benchmarks tailored to your level of expertise.
Market Insights and Trend Forecasts:
Beyond salaries, our guide offers invaluable market insights from industry leaders and our experts. We dissect the trends that shaped the tech job market in 2023, emphasising key drivers and challenges across both the permanent and contract sectors. From emerging technologies to shifts in hiring trends, we anticipate the developments that will influence wages and roles high in demand. Whether it's the increasing importance of cybersecurity or the growing demand for AI integration, our guide provides you with the knowledge to navigate the UK tech job market effectively.
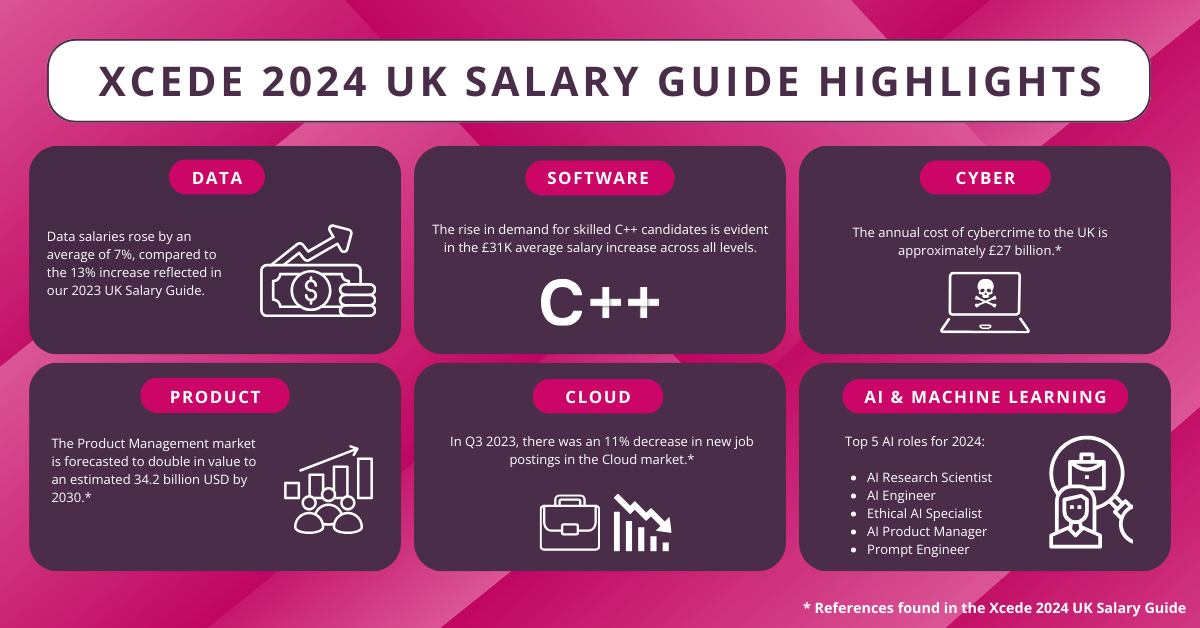
See below some key highlights from this year’s Salary Guide:
Highlighting our Specialisms:
Diving deeper, our guide shines a spotlight on each of our specialisms, offering an expert understanding of nuances within the roles across Data, AI & Machine Learning, Product, Software, Cloud, Cyber, and C-Suite levels. Whether you're curious about the latest trends in data analytics or seeking to understand the evolving responsibilities of CDOs and CIOs, our guide covers it all.
Fill out the form and download your copy today!